The following essay is reprinted with permission from The Conversation, an online platform protecting cutting-edge research. The Conversation
U.S. Military officers have been these days caught off defend with the aid of revelations that servicemembers’ virtual health trackers had been storing the locations of their exercises, such as at or near navy bases and clandestine websites around the sector. But this threat isn’t restricted to Fitbits and similar gadgets. My institution’s current studies have shown how cellular telephones also can track their users via stores and towns and around the world—even when users flip off their telephones’ location-tracking services.
The vulnerability comes from the extensive range of sensors phones are equipped with—not just GPS and communications interfaces, but gyroscopes and accelerometers, which could tell whether or not a smartphone is being held upright or on its side and can degree other moves too. Apps on smartphones can use the one’s sensors to carry out duties customers aren’t watching for—like following a user’s actions turn by turn along city streets.
Related Posts :
- 11 Tips for Managing Your Pro Tools Sessions
- TFG now gives clients cyber coverage for cellular gadgets
- Mobile gadgets could improve
- Mobile devices are even extra vulnerable
- Building Your Small Business Website
Most people anticipate that turning their phone’s location offerings off disables this form of cell surveillance. But the research I behavior with my colleagues Shashank Narain, Triet Vo-Huu, Ken Block, and Amirali Sanatinia at Northeastern University, in a discipline referred to as “aspect-channel assaults,” uncovers approaches that apps can avoid or break out those restrictions. We have found out how a smartphone can eavesdrop on a consumer’s finger-typing to discover a mystery password—and the way virtually carrying a smartphone in your pocket can inform information organizations where you are and where you’re going.
MAKING ASSUMPTIONS ABOUT ATTACKS
When designing safety for a tool or a device, people make assumptions approximately what threats will arise. Cars, as an instance, are designed to guard their occupants from crashes with other vehicles, buildings, guardrails, phone poles, and other objects usually found in or close to roads. They’re not designed to hold humans secure in automobiles pushed off a cliff or smashed by massive rocks dropped on them. It’s just now not price-effective to engineer defenses towards those threats, due to the fact that they’re assumed to be extraordinarily uncommon.
Similarly, humans designing software programs and hardware make assumptions about what hackers might do. But that doesn’t imply devices are secure. One of the first aspect-channel assaults was diagnosed back in 1996 by cryptographer Paul Kocher, who confirmed he could damage popular and supposedly secure cryptosystems by carefully timing how long it took a computer to decrypt an encrypted message. The cryptosystem designers hadn’t imagined that an attacker could take that method, so their gadget became susceptible to it.

There have been many different attacks over time the using all forms of unique strategies. The latest Meltdown and Spectre vulnerabilities that make the most layout flaws in laptop processors are also facet-channel attacks. They permit malicious packages to eavesdrop on other applications’ information in the laptop’s memory.
MONITORING ON THE GO
Mobile gadgets are ideal targets for this kind of attack from an unexpected source. They are filled with sensors, typically together with at least one accelerometer, a gyroscope, a magnetometer, a barometer, as many as 4 microphones, one or cameras, a thermometer, a pedometer, a mild sensor, and a humidity sensor.
Apps can access most of these sensors without asking for permission from the person. And by way of combining readings from or extra gadgets, it’s frequently feasible to do things that users, phone designers, and app creators alike might not assume.
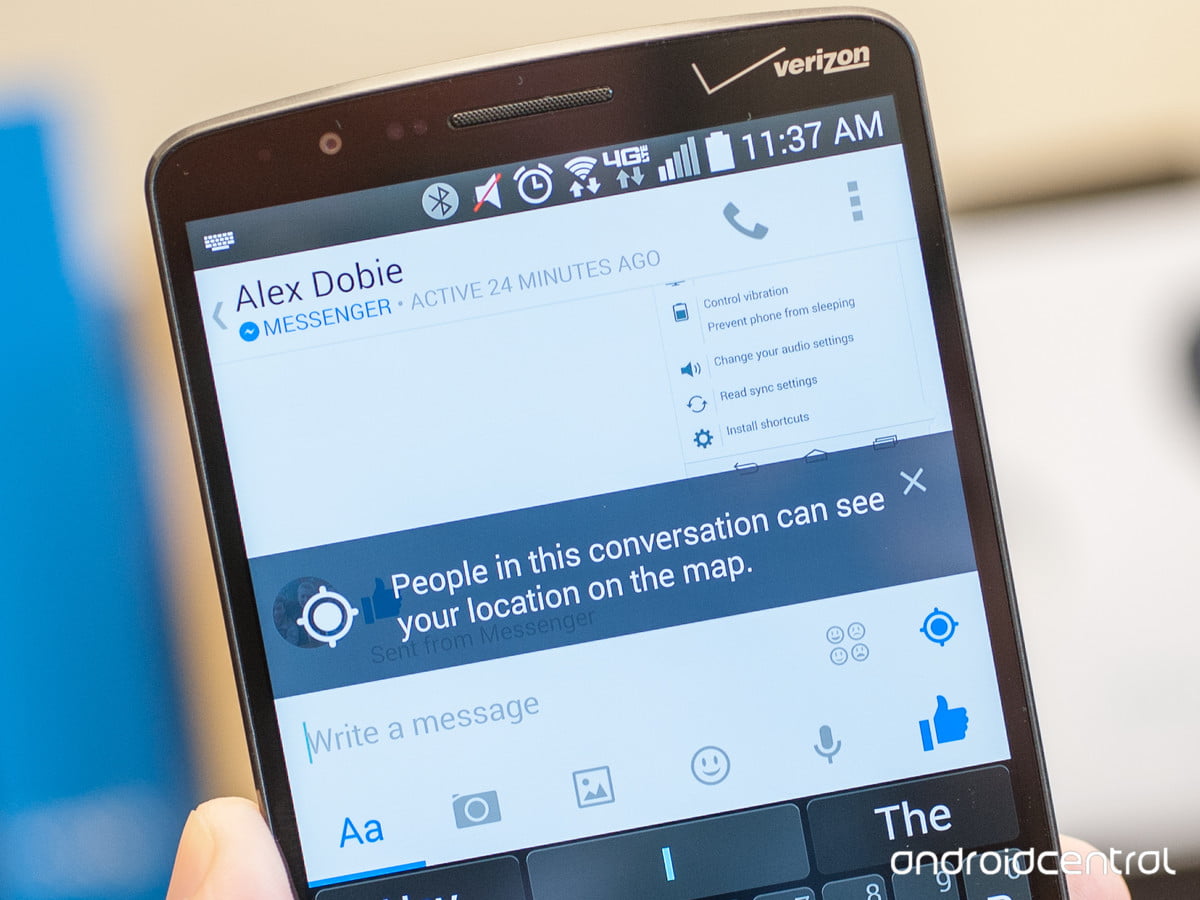
In one current task, we developed an app that might determine what letters a user was typing on a cellular cellphone’s on-screen keyboard, without reading inputs from the keyboard. Rather, we mixed records from the telephone’s gyroscope and its microphones.
When a person taps on the screen in specific locations, the telephone itself rotates slightly in methods that may be measured via the 3-axis micromechanical gyroscopes observed in modern phones. Further, tapping on a smartphone display produces a sound that can be recorded on every one of a smartphone’s more than one microphones. A tap near the middle of the display screen will not circulate the telephone’s sound, will reach both microphones at the same time, and will sound more or less equally to all of the microphones. However, a faucet at the lowest left edge of the display screen will rotate the smartphone left and down; it’s going to attain the left microphone quicker, and it’ll sound louder to microphones near the bottom of the display screen and quieter to microphones somewhere else on the tool.
Processing the motion and sound facts together lets us determine what key a person pressed, and we were correct over 90 percent of the time. This kind of character might be introduced secretly to any app and will run disregarded by a user.
IDENTIFYING A LOCATION

We then puzzled whether or not a malicious utility should infer a person’s whereabouts, including where they lived and worked, and what routes they traveled—statistics that most people don’t forget are very private.
We desired to find out whether a user’s region may be identified using the use of handy sensors that don’t require users’ permission. The route taken by a driver, for example, may be simplified into a series of turns, each in a certain route and with a certain attitude. With every other app, we used a phone’s compass to look at the man’s or woman’s course of the journey. That app extensively utilized the cellphone’s gyroscope, measuring the sequence of flip angles of the course traveled by the consumer. And the accelerometer showed whether or not a person stopped or transferred.
By measuring a sequence of turns and stringing them together as someone travels, we may want to make a map of their actions. (In our paintings, we knew which city we had been tracking human beings via, but a comparable approach may be used to determine what city someone was in.)
Imagine we study someone in Boston heading southwest, turning one hundred ranges to the right, making a sharp U-flip to the left to head southeast, turning barely to the proper, continuing directly, then following a shallow curve to the left, a short jog to the proper, bumping up and down more than normal on a road, turning 55 degrees right, and turning 97 degrees left and then making a mild curve proper before stopping.
We evolved a set of rules to shape those moves up in opposition to a digitized map of the streets of the city the user is in, and determined which were the maximum possible routes a person may take. Those movements should discover a path driving from Fenway Park, along with the Back Bay Fens, beyond the Museum of Fine Arts, and arrive at Northeastern University.