One of the fascinating mobile video games of the 12 months was just given a launch date as Square Enix announced that Final Fantasy XV: Pocket Edition will launch on February 9th. Unveiled at Gamescom closing summer time, FFXV: Pocket Edition is a remake of the original console and PC game with touch controls and cell-suitable portraits.
A decade after its unveiling, Final Fantasy XV finally launched on PS4 and Xbox One at the cease of 2016. It was later ported to PC as well, but now cellphone and tablet owners are going to have a hazard to experience the journey in miniature form. The Pocket Edition will tell the same tale because the unique sport, cut up into 10 chapters.
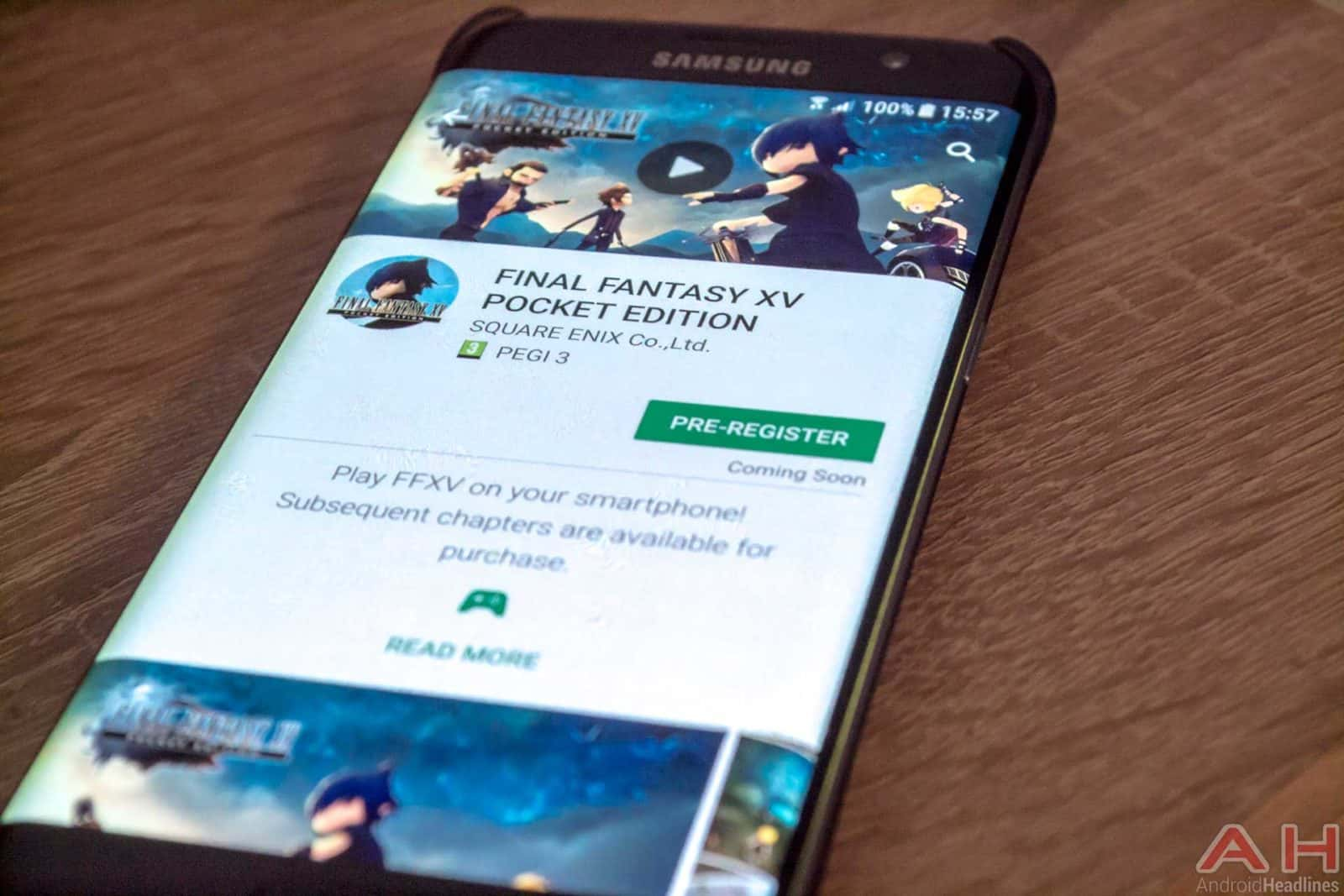
Unlike many of Square Enix’s cellular games, Final Fantasy XV: Pocket Edition might be loose to download. That consists of the primary of ten chapters at no cost, but you’ll need to pay for the rest. Chapters 2 & 3 might be $0.Ninety-nine a bit, whilst the ultimate seven chapters will cost $2.99 a pop. You can also buy all ten chapters at once for $19.99. All ten chapters may be had as in-app purchases on the day the app arrives on iOS and Android.
To run the game, you’ll want either an iOS device running iOS eleven.1 or later, or an Android device running Android 5. Zero Lollipop or later. You can see all the specification requirements on Square Enix’s game web page.
Related Posts :
- 11 tips to prevent phishing
- NOC is obligatory for asset registration
- The EOS blockchain operating system unveils a year-long token distribution
- Is the wildly popular WordPress a conduit to compromise?
- Templates of Denial Selective History
If you missed out on Final Fantasy XV when it hit consoles over a year ago and need to see what all of the fuss was about, this is a laugh-sized model that promises to recount everything critical from the original game.
Cell phones like iPads can now be located in even the smallest companies, making it important for IT managers to engage in mobile device management. If employees aren’t taking their private mobiles to work (BYOD), employers are providing these devices, creating challenges for IT managers tasked with protecting company networks from unauthorized use. On any given day, the IT body of workers won’t realize how number or what type of gadgets are having access to their networks, creating a very dangerous situation.
The Mobile Device Management Challenge
An unmarried employee who accidentally exposes the enterprise to a network safety breach can cripple operations and even incur regulatory consequences. This gives a pretty mission for the IT group of workers, because of this, it additionally creates an opportunity for groups that provide a solution. These groups help groups control and secure cellular gadgets with authorized get right of entry to to corporate networks. There is a good deal of ability in this line of work because the state of affairs will simply become to be extra complicated as the recognition of smartphones come to be popular furniture in the place of business.
IT managers ought to sell the secure use of laptops, tablets, and smartphones, whether these are for my part owned or enterprise-provided. Otherwise, the safety breach or leak can be catastrophic. While some employers at the start banned individually owned gadgets from the place of work, they’ve quickly realized that that is, not least, impractical and in most instances, impossible. The state of affairs is complicated by the reality that many employees use those gadgets to perform their jobs.
The Mobile Device Management Solution

A new aspect of the IT channel has developed, and it’s referred to as the mobility management provider or MMSP. It encompasses consulting offerings designed to establish the place of work cell tool regulations, management, and security. These services help business customers put in force a at ease platform for all cellular devices, which is compliant with statistics storage, restoration, use, and transmission. Providers of those solutions need to harness the opportunities offered by using these surroundings to develop solutions for agencies of all sizes.
These answer companies aren’t without outside sources. The Computing Technology Industry Association, referred to as CompTIA, is lending a helping hand via growing assets and schooling packages geared in the direction of business enterprise-extensive lodging of mobile devices. It has advanced an advisory board proposing smartphone manufacturers, providers, application developers, and solution vendors with a view to assisting direct its schooling projects.
However, solution carriers need to not watch for an application from CompTIA. They should attain out to corporations, helping them to manage mobile fleets and shield their networks. Through this collaboration, IT managers can increase corporation guidelines concerning the use of private cell phones and other smart gadgets. They also can be satisfied to at ease these devices or issue gadgets owned by the agency.
Several advantages are found when paying to make a private mobile phone at ease. IT managers defend the corporation and offer workers a fee-based advantage. Though effort and time are required to manipulate cell gadgets in the place of work, those are justified. Solution companies offering device control offer the framework required to make the activity simpler for IT managers who already have an excessive amount on their plates.
The dual USB automobile charger is a superb instance of how a product has evolved as a response to satisfy the wishes of people who use portable electronic cell telephones and devices. Portable is the operative word in this instance, and those devices possess some not-unusual capabilities. For this newsletter, the most critical commonplace characteristic is that they all require charging. They require a charging answer, as well as the devices themselves, so that complete capability at any given time is always to be had. A useless tool is a little need for its customers.
The Cell Phone Car Charger

The underlying assumption with this charger is that mobile telephone users additionally use a car. In the general public of cases, this is precisely what takes place, and the car may be your personal use car or an agency vehicle that you use throughout a typical workday. The cell phone charger for a vehicle is small enough that you can hold it available in a pocket so that you can use it in a couple of automobiles as required. Of course, it’s far appropriate to be used in a couple of vehicles without the opportunity of causing harm to the car’s electrical device, so it has familiar usability.