Surat, Feb three (PTI) Two fair charge store proprietors were arrested by the Crime Branch here for allegedly diverting subsidized grains using duplicate software and unauthorized biometric records of beneficiaries.
Police stated that Babubhai Boriwal (fifty-three) and Sampatlal Shah (sixty-one) were arrested the day before and were sent to police custody for 5 days.
Explaining the modus operandi, Crime Branch Inspector BN Dave stated, “The national government had in April 2016 released the Annapurna Yojana under the National Food Security Act-2013. Fair fee shops, renamed as Pandit Deendayal Grahak Bhandar, had been computerized so that subsidized food items reached the actual beneficiaries.”
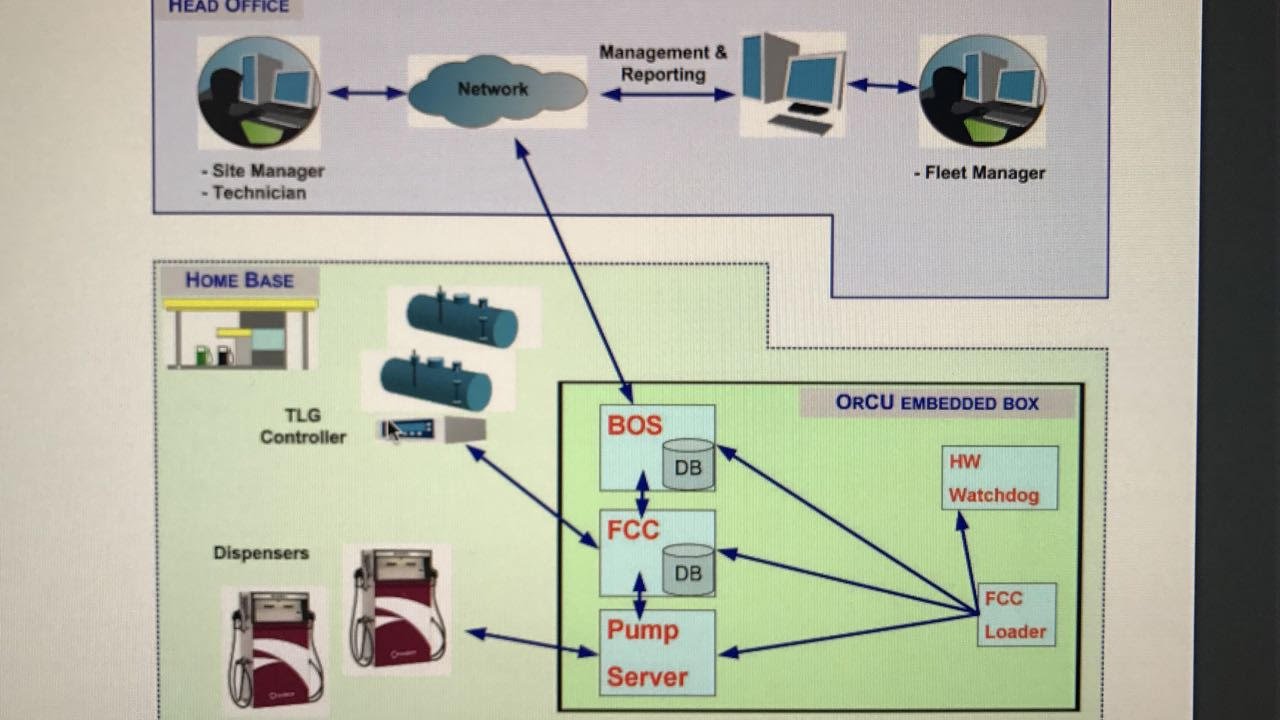
Dave said that truthful fee shops had been supposed to use an application called E-FPS, provided by the authorities, with a database of beneficiaries fed into it.
He delivered, “As part of this, honest charge, save owners had been given a username and password to get admission to the biometric information bank of beneficiaries to create an electronic record of beneficiaries availing subsidized grains from their shops.”
“The beneficiary had to provide his fingerprint, info about his ration card, and UID (Aadhaar) numbers to shape the information fed into the pc. This could generate a slip on the idea of which he became given a subsidized ration each month,” Dave stated.
The arrested duo, he said, used duplicate software and received information on financial institutions of beneficiaries from an unknown source.
“They used this statistics bank to create an electronic document each month to show that beneficiaries had received subsidized foodgrains while in reality, they had not,” he said.
Dave stated that investigations had been underway to find out the source of the fake software and the biometric information.
Earlier, eight separate FIRs were lodged against as many truthful prices save proprietors inside the metropolis following research conducted with the district administration’s aid after some beneficiaries complained. The report was turned in and then handed over to the Crime Branch.
Police said that the 2 were booked under numerous sections of the Indian Penal Code (IPC), such as section 406, 409 (crook breach of agree with), 467, 468, 471 (forgery), in addition to sections of the Information Technology Act and the Essential Commodities Act. PTI KA BNM
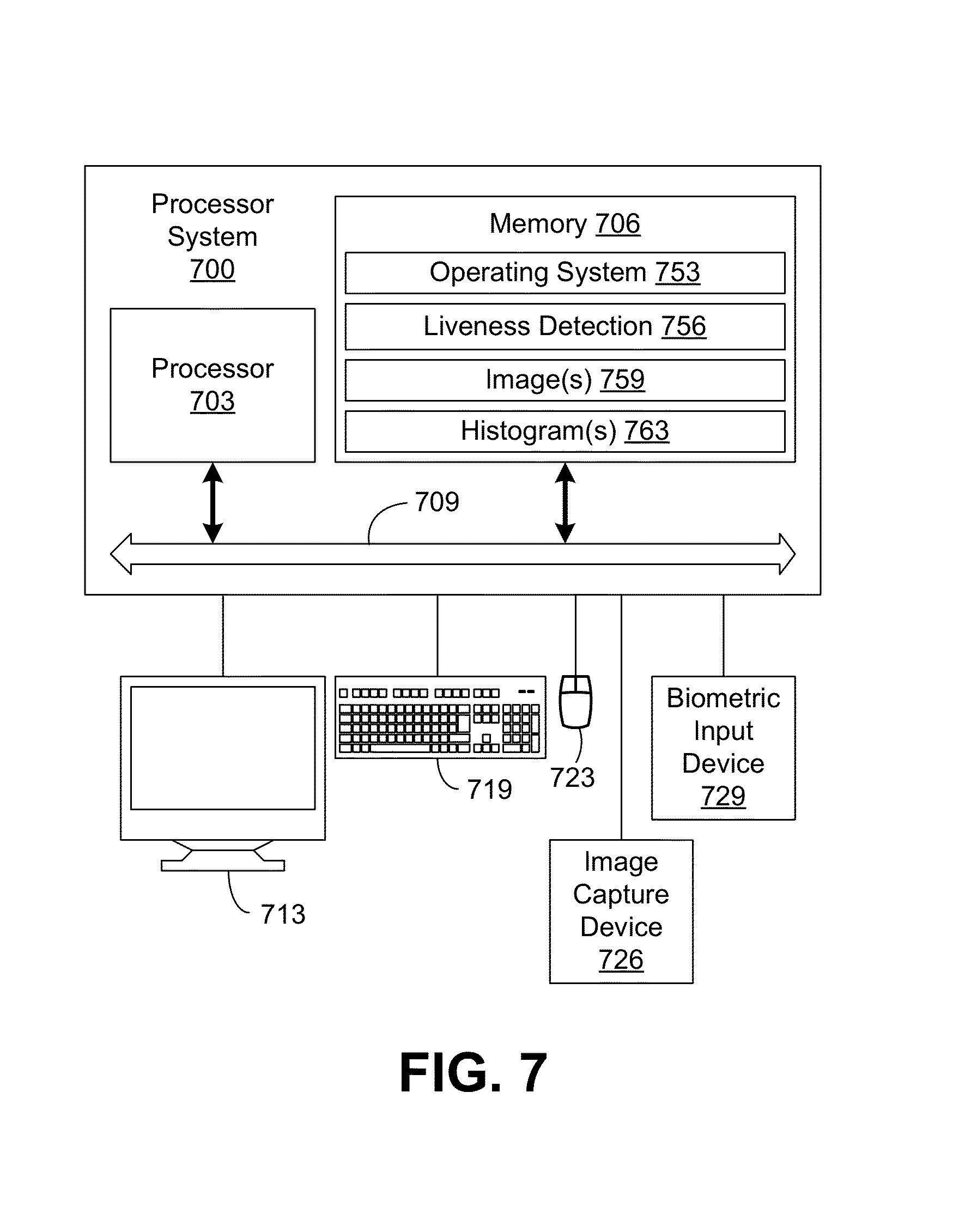
A biometric identity machine can identify humans via their traits. There are special varieties of physiological biometric identification software programs. These software programs can be grouped on the premise of the physical function they perform. Biometric identity is advanced than other identity techniques because it examines one’s traits that cannot be easily shared or stolen.
Types of Biometric Identification Software
Face Recognition
Face popularity software systematically examines precise features not unusual to all human faces, together with the separation between eyes, the position of cheekbones, and the jawline. After reading all of the numerical quantities, the software program combines them in a single code.
Hand Geometry Biometrics
Hand geometry reading usually takes place in harsh environments, may be performed in unclean situations, and produces a minimal dataset. The reading is not considered intrusive. The hand geometry test is generally the favored technique of identity in business environments.
Fingerprint Recognition
A fingerprint scanner is a leading technology of the biometric era, and they’re already a part of a few laptops and PDAs, inclusive of the iPaq Pocket PC. Traditionally, fingerprint analysis changed into accomplished by highly educated experts. The biometric identity software program does the same activity, though it uses a computer to examine a virtual image to identify a person. Such a software program examines the pattern of ridges and furrows present on the character’s fingertips and the minutiae points of a specimen print with other prints in its database. Fingerprint evaluation has been occurring for the past 140 years, and up to now, nobody has determined prints that might be exactly equal. With age, hands develop in size, but the relationship between the ridges no longer holds.
Retina Scan
Replicating a retina is considered impossible because the blood vessels gift at the back of the eye to form a unique sample. A retina experiment requires about 15 seconds of cautious concentration. This method continues to be widespread in navy installations.
Iris Scan
Iris scanning additionally supplies precise records that can’t be duplicated without difficulty. The trouble stage of the test is just like a retina experiment.
Signature
Signatures are some other sort of records that are not bodily intrusive and can be without problems accumulated using a suitable biometric authentication software program. Some humans use digitized signatures. However, such signatures generally do not have the resolution to ensure authentication.
Voice Recognition
Voice popularity is much like face recognition because it provides authentic identification without the person’s knowledge. It is easier to cheat in this look at (with recorded voice); it is impossible to trick an analyst by speaking like someone else.
Human resource management isn’t always an easier assignment, especially when you are managing an enterprise with heaps of personnel and many regular daily visitors. In massive agencies, it’s miles difficult to screen the activities of your employee and a number of the basic assignment like marking the IN and OUT time of the worker, how an awful lot of time he remains within the office, and what sort of going away specific employee has taken so that you can create a file on the cease of the month and represent this document to the management of the enterprise and additionally calculate personnel earnings and other matters which are associated with depart policies. In this form of group with masses of personnel, there should be a machine that tracks the tasks that I have explained above automatically and appropriately without a single mistake. Here, I need to give the fundamental creation of these forms of the machine that may reduce your agency’s effort in HR management.
As I have stated before, tracking your employee Time, Attendance, and site visitors is a critical and time-consuming project. It became almost impossible to control employees’ attendance or tourist access manually with a log system in the database for massive businesses. For employees, we want to have a gadget that tracks their IN time and OUT time, and in an equal way, for visitors, it should store some of the primary statistics which ought to be accessed effortlessly in the future. Along with monitoring the entries as they should be, it also promises the security of your premises, so you may be free from worrying about the premises’ safety.