How Secure Is Your Operating System?
Ever wonder how comfortable your information truly is? What safety protocols do you exercise? Maybe growing a password? Locking the PC so others can not gain access to your statistics? Bypassing Windows passwords best takes a minute or less, and the Windows 10 installation disk. In Thus ways, I had been a hit in the use of the Windows 10 disk to pass account passwords and even activating deactivated debts on Windows Server 2012, Windows 10, Windows 7, and Windows eight.1. I have yet to check the technique to pass locked computer accounts in Windows XP and Vista. However, I do no longer foresee any complications with those running structures.

Before you suspect this makes you safer because you use Mac OS X, I have also been able to pass root-level account passwords on a MacBook Pro, running Mac OS X (10.10) Yosemite running device, the use of built-in Apple commands. This technique also took less than a minute to accomplish.
Related Posts :
- New Update to Windows Template Studio
- When Corruption Is the Operating System: The Case of Honduras
- This web design bundle will teach you everything from HTML to Flash.
- Windows 10 S Review: Pros and Cons of New Microsoft Operating System
- Facebook Updates News Feed to Reduce Spam and Fake News
The safety implemented in a running device and bills constantly has a stage of vulnerability. Most security features are excellent techniques. Username and passwords, for instance, represent single-factor authentication, identifying who you are, the username, and proof that you are who you are, the password. It is said that current protection protocols require the username to be specific and the password to have at the very least 16 characters and a random combination of uppercase, lowercase, numbers, and special characters to be utilized.
16 digits is the extent to of the common individual to keep in mind their passwords. With the developing technological advancements of computer processing power, such passwords will ultimately be compromised in shorter quantities of time, eventually making them useless. Most operating systems keep username and password mixtures as hash algorithms in precise documents that may be considered as plain textual content, ensuring within the want for passwords to be in the long run obsolete.
Stating those statistics does not suggest “So, why the hassle?” with usernames and passwords. Passwords prevent the common man or woman from gaining access, and a few levels of protection are higher than no level of safety. There, of course, are different ways to more securely protect your operating systems, preventing the approach cited here from being able to be applied. Data at rest encryption, as an example, is a choice at the operating system level. In this manner, a decryption system should arise before the working system boots.
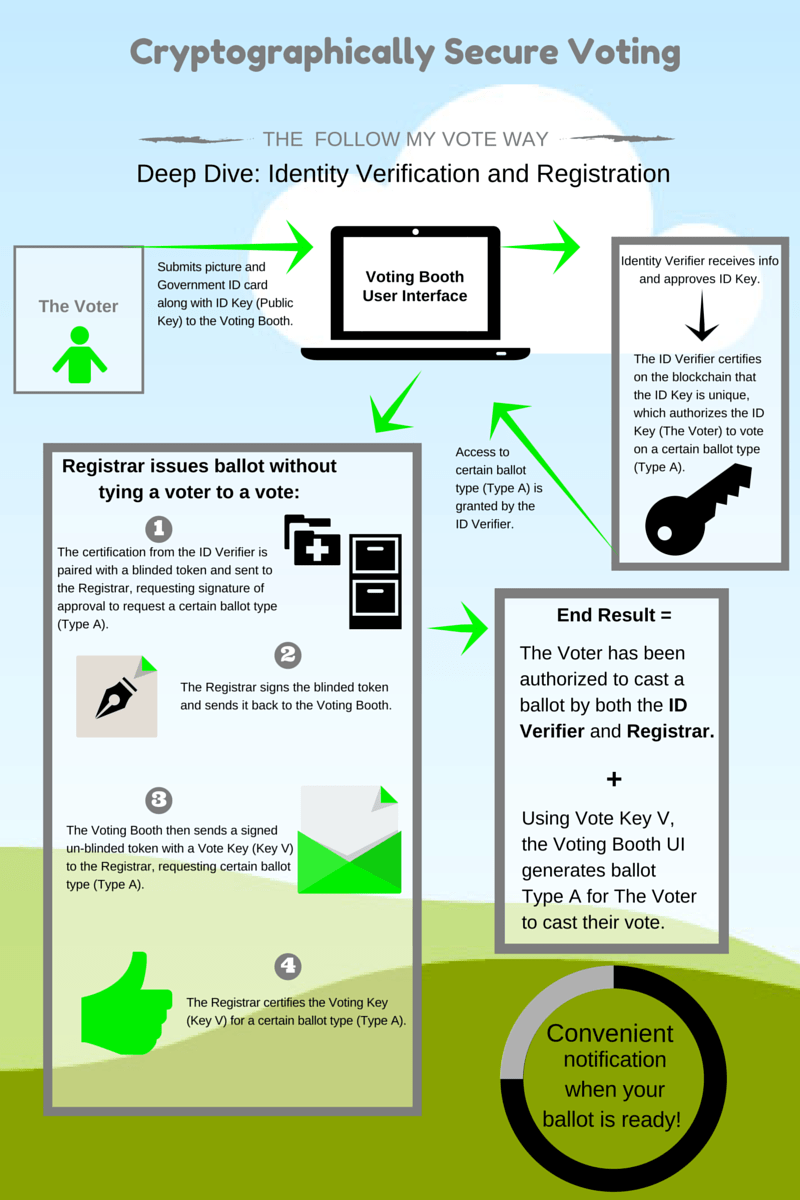
2 things and three-component authentication additionally increase the security stage of your operating system. CAC (Common Access Cac) playing cards, normally utilized by the DoD and other government agencies, are a prime example of two-factor authentication. The first component, requiring the cardboard itself, keeps an encrypted certificate to discover who you are and who you say you are, plus the second factor of a PIN as secondary proof. 3-issue authentication might encompass capabilities, including biometrics. Keep in mind, despite all of those methods being applied. There isn’t any such aspect as a one-hundred percent relaxed machine.